Secret management practice pattern
Practical operation guide that reduces the risk of confidential information exposure by combining environmental variables, vault, and KMS

Introduction
Most secret leak incidents originate from operational mistakes rather than advanced hacking. When copying environment variable files, outputting logs, and hard-coding test codes accumulate, small mistakes can lead to major accidents. This article organizes storage, distribution, rotation, and audit procedures into practical standards from a secret life cycle perspective.
Problem definition
Secret management is not solved by just selecting a tool. Organizational rules and automation must go together.
- Development/staging/production secrets are not separated, so permission boundaries are broken.
- The rotation period is not defined, so long-term keys are left unattended.
- It is difficult to track leaks due to lack or lack of access logs.
The most important principles are least privilege and short lifespan. The structure of distributing long-term secrets to people must be eliminated.
Key concepts
| perspective | Design criteria | Verification points |
|---|---|---|
| Save | KMS/Secret Manager centralization | Number of plaintext saved files |
| Distribution | runtime injection | Whether to include build output |
| rotation | Automatic replacement schedule | Rotation completion rate before expiration |
| thanks | Access event log | Abnormal access detection time |
The secret strategy must be tied to the application architecture. Unifying the secret injection path in your deployment pipeline reduces the risk of omission and exposure.
Code example 1: Runtime secret injection
export async function getDbCredentials() {
const secret = await secretClient.access({
name: "projects/8space/secrets/db-prod/versions/latest",
});
const payload = JSON.parse(secret.payload);
return {
host: payload.host,
user: payload.user,
password: payload.password,
};
}
Code example 2: Secret rotation placement
#!/usr/bin/env bash
set -euo pipefail
SECRET_NAME=$1
./scripts/secret/create-version.sh "$SECRET_NAME"
./scripts/secret/redeploy-services.sh "$SECRET_NAME"
./scripts/secret/verify-access.sh "$SECRET_NAME"
./scripts/secret/disable-old-version.sh "$SECRET_NAME"
Architecture flow
Tradeoffs
- Centralization enhances security, but requires initial setup and establishment of operating standards costs.
- Auto-rotation reduces the risk of accidents, but increases the frequency of service redistribution.
- Leaving detailed access logs makes analysis easier, but log storage costs increase.
Cleanup
Secret management is not about hiding files, but about life cycle design. By connecting central storage, runtime injection, automatic rotation, and audit logs, operational risks can be structurally reduced.
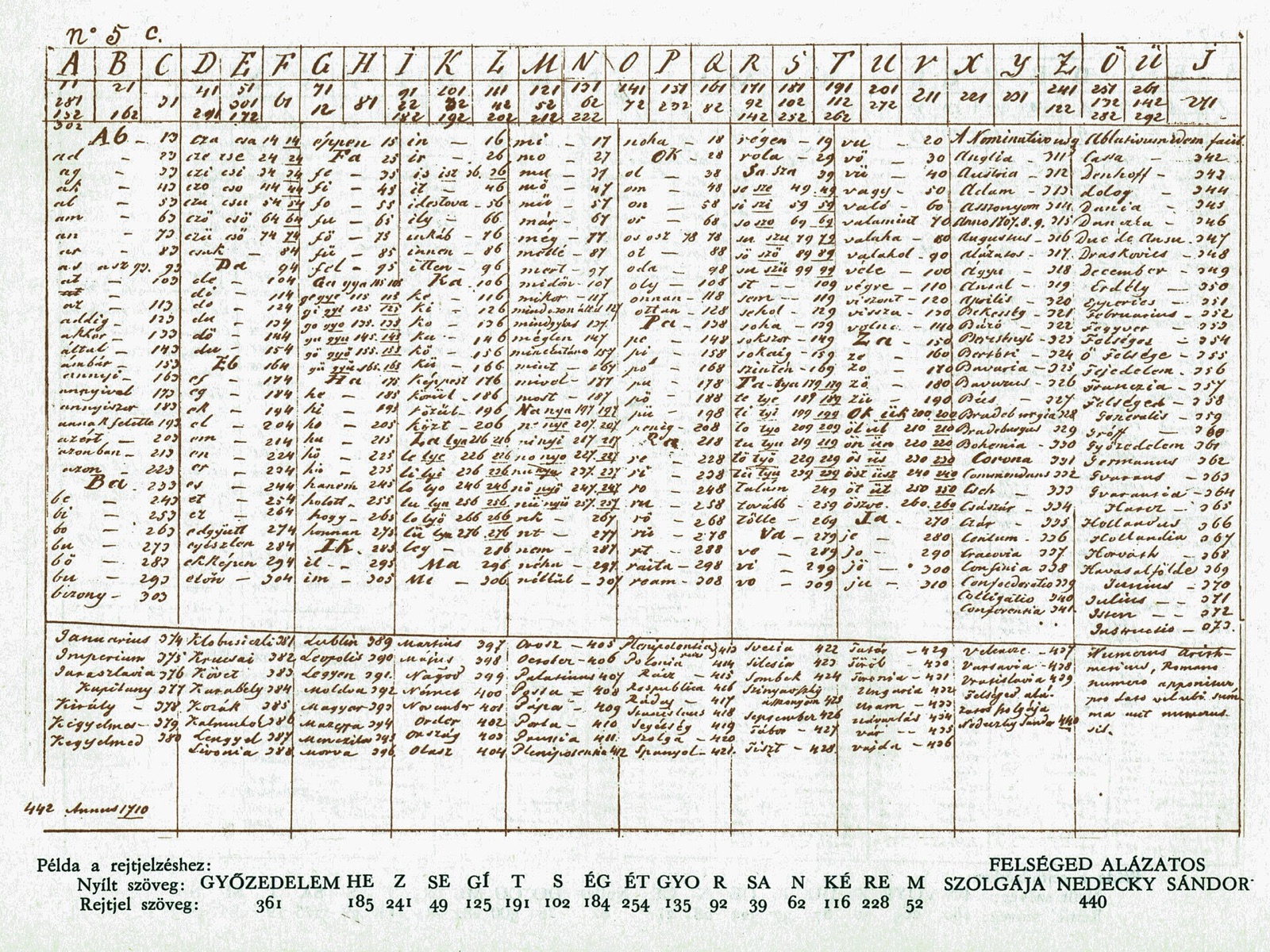
Image source
- Cover: source link
- License: Public domain / Author: Own work
- Note: After downloading the free license image from Wikimedia Commons, it was optimized to JPG at 1600px.